Why emails—not transactions—are now the weakest link
By ICTpost Cyber Intelligence Bureau
Modern financial fraud is no longer confined to the moment a payment is initiated. Instead, it unfolds over days or weeks through domain manipulation, email thread hijacking, identity compromise, and behavioral deception—often escaping traditional transaction‑centric controls. Recent global data shows that business email compromise (BEC) and related social‑engineering attacks remain among the most costly cyber‑enabled crimes worldwide. This article examines how such frauds evolve, why legacy defenses fail, how artificial intelligence has accelerated attack sophistication, and what organizations must do—practically and structurally—to detect and prevent fraud earlier in the attack lifecycle.
A Payment That Looked Legitimate
In 2024, a multinational financial institution approved what appeared to be a routine vendor payment. The invoice matched historical records. The email thread appeared authentic. The request carried plausible urgency.
The payment—approximately USD 3 million—was later confirmed as fraudulent.
No transaction‑monitoring alert was triggered. No anomaly was identified at the point of payment. The reason was simple: the fraud had already occurred days earlier.
Where Modern Fraud Really Begins
Investigation showed that the attack followed a now‑common pattern:
- Look‑alike domain registration
A domain visually similar to a trusted vendor’s address was registered days in advance. - Conversation hijacking
Attackers inserted themselves into an existing email thread (often called thread hijacking or vendor email compromise), leveraging previously stolen credentials. - Payment detail manipulation
Bank account information was subtly changed while preserving legitimate invoice structure.
By the time money moved, the attack was already complete.
As Bernard Marr notes in his analysis of fraud evolution:
“Fraud rarely announces itself when money moves—it usually leaves clues much earlier, hidden in signals many organizations still fail to connect.”
— Bernard Marr, Why Threat Intelligence Is Becoming a Must‑Have in Fraud Prevention [deloitte.com]
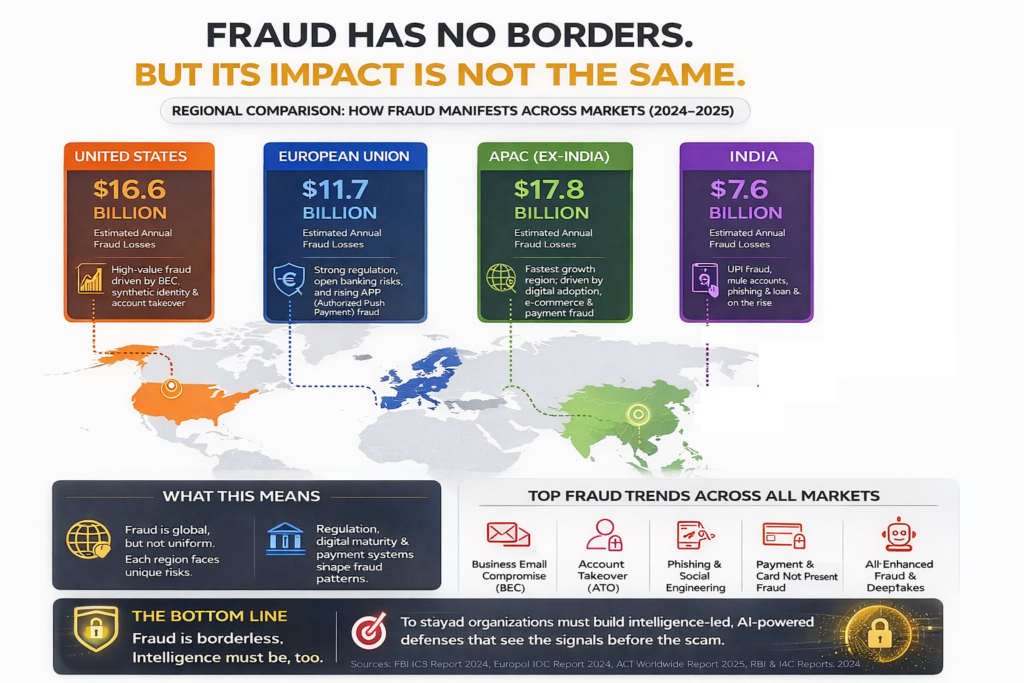
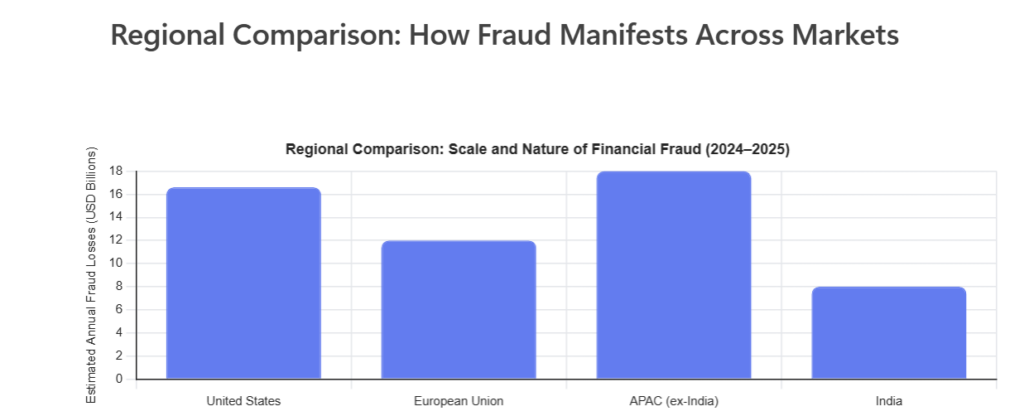
The Scale of the Problem: What the Data Shows
According to the FBI Internet Crime Complaint Center (IC3) 2024 Annual Report:
- Total reported cyber‑enabled fraud losses (2024): USD 16.6 billion
- Business Email Compromise (BEC) losses (2024): approx. USD 2.77 billion
- BEC losses (2022–2024): nearly USD 8.5 billion globally
- 83% of total reported losses involved cyber‑enabled mechanisms
📄 Source: FBI IC3 2024 Annual Report (PDF)
👉 https://www.ic3.gov/Media/PDF/AnnualReport/2024_IC3Report.pdf
Industry surveys reinforce the trend:
- Over 95% of BEC incidents begin with phishing or domain spoofing
- Look‑alike domain attacks and invoice fraud increased sharply between 2023–2025
- An estimated 40% of BEC emails in 2024–25 were AI‑assisted
Sources include AFP, Hoxhunt, VIPRE, and Proofpoint research.
Why Transaction‑Focused Fraud Controls Fall Short
Traditional fraud prevention assumes risk is visible at the point of payment. That assumption no longer holds.
Modern fraud is is process‑driven, not based on a single sudden event, which means it unfolds gradually through a series of connected steps. It usually begins with quiet research, where attackers study a company’s domain, people, and communication patterns. They then try to obtain login details, often through phishing or reused passwords, which allows them to slip into real email accounts. Once inside, they patiently watch and take over ongoing email conversations, making their messages appear normal and trusted. Over time, they imitate the writing style, timing, and behavior of the real person so nothing seems suspicious. Only in the final stage do they attempt financial manipulation, such as changing payment details or requesting urgent transfers. Because each step looks harmless when viewed alone, most organizations only notice the attack at the very end, when money is already at risk.
As cybersecurity strategist Dr. Chase Cunningham summarizes: “If you’re waiting for a transaction alert, you’re already late.”
The Role of Artificial Intelligence
Generative AI has dramatically lowered the cost and skill required to conduct convincing fraud:
- Emails are grammatically and contextually accurate
- Voice and video deepfakes enable executive impersonation
- Fraud workflows are automated at scale
Deloitte estimates that AI‑enabled fraud could drive U.S. fraud losses to USD 40 billion annually by 2027, more than triple 2023 levels. [ic3.gov]
Stanford AI researcher Fei‑Fei Li has consistently emphasized the broader implication:
“AI’s power lies in its ability to mimic and scale human behavior.”
In fraud, that capability directly undermines identity‑ and activity‑based trust.
Regional Patterns: Fraud Is Global, but Not Uniform
While fraud techniques are shared globally, impact and patterns vary:
- United States: High‑value BEC, executive impersonation, deepfake‑enabled scams
- European Union: Lower loss per capita due to strong regulation (PSD2, SCA), but high cross‑border attack volume
- APAC: Fastest growth, driven by platform ecosystems and mobile payments
- India: Real‑time payments (UPI) shift fraud upstream to social engineering and mule networks
What Global Best Practice Looks Like: Prevention, Not Just Awareness
High‑quality global guidance goes beyond “be vigilant.” Leading organizations implement layered, verifiable controls:
1. Email and Domain Security
Email and domain security is about making sure that emails really come from who they claim to come from and stopping fake but convincing messages early. Tools like DMARC, SPF, and DKIM help email systems verify that messages sent in the company’s name are genuine and not forged. At the same time, organizations need to watch for fake domains that closely resemble their real domain, because attackers often use these look‑alike addresses to trick people. Extra caution is needed for financial actions, so emails or requests coming from newly created domains are blocked by default until they are verified. Together, these steps reduce the chances of attackers slipping in through email and quietly building trust over time.
Reference: Proofpoint, Abnormal Security best practices. [CodeInterpreter | Undefined]
2. Payment Verification Controls
- Mandatory out‑of‑band verification (voice or portal‑based) for:
- Vendor bank detail changes
- Payment urgency overrides
- Dual approval with role separation, not just hierarchy
3. Behavioral and Contextual Signals
- Detect:
- Email thread anomalies
- Login behavior deviations
- Cross‑market attack patterns
Organizations like Mastercard now integrate cyber and fraud intelligence to intervene before customers are affected. [salesso.com]
4. Organizational Alignment
Organizational alignment means that different teams in the company work together instead of in isolation when dealing with fraud and cyber risks. Fraud, cybersecurity, and compliance teams regularly share what they are seeing, such as suspicious patterns, incidents, and trends, so everyone has the same understanding of the threat. When an incident happens, the focus is not only on recovering lost money or fixing the final problem, but on going back to identify the earliest warning sign that could have been detected. This helps the organization improve its defenses earlier in the process and prevent similar attacks from progressing in the future.
Why This Matters Beyond Financial Loss
Fraud incidents increasingly carry:
- Regulatory consequences
- Reputational damage
- Long‑term erosion of customer trust
In a digital economy, trust—not capital—is the most fragile asset.
Anticipate Fraud
The executive who approved that USD 3 million payment did not “miss” fraud. The system did—by focusing on the wrong moment.
Fraud today rarely begins with a transaction.
It begins with a domain, an email, a behavior change—often days or weeks earlier.
Organizations that adapt their defenses to this reality gain a decisive advantage: they do not merely detect fraud.
They anticipate it.
References
Hoxhunt / VIPRE / AFP Fraud Research [CodeInterpreter | Undefined], [nacha.org]
FBI IC3 2024 Annual Report (PDF): https://www.ic3.gov [CodeInterpreter | Undefined]
Bernard Marr, Why Threat Intelligence Is Becoming a Must‑Have: https://bernardmarr.com [deloitte.com]
Deloitte Center for Financial Services, AI Fraud Analysis: https://www.deloitte.com [ic3.gov]